Architecture #
General #
The uman platform is built on top of Google Cloud.
The following diagram depicts the high-level architecture with its main components:
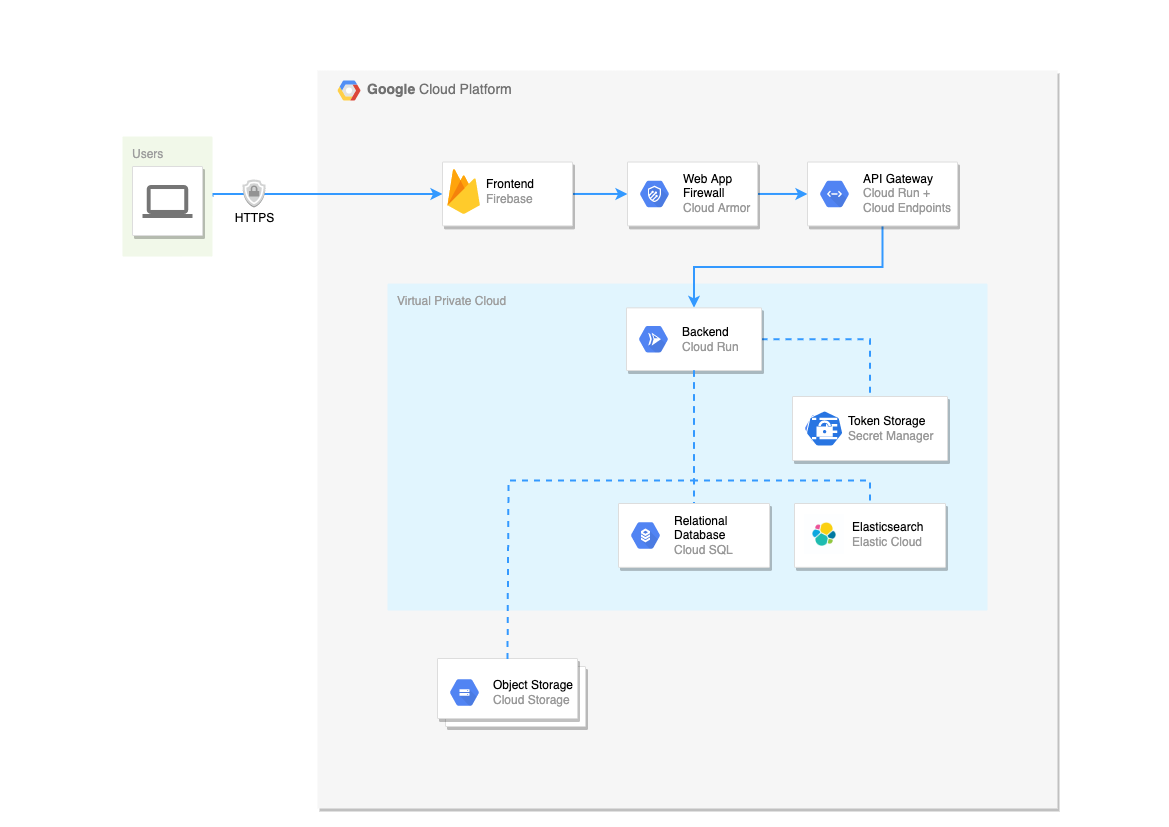
- Frontend: provides the user the web application HTML and scripts, hosted on Firebase.
- Web application firewall (WAF): helps protect the application against denial of service and web attacks. Google Cloud Armor is leveraged here to benefit from DDoS protection and WAF at Google Scale. This includes mitigation against OWASP Top 10 risks.
- API Gateway: protects and monitors the backend API. Incoming traffic is protected based on the OpenAPI specification of the backend API, meaning that only the specified routes are accepted by the gateway. Google Cloud Endpoints is used in combination with Cloud Run to host the API Gateway.
- Virtual Private Cloud (VPC): acts as an isolated network that is not publicly accessible.
- Backend: provides the necessary information and search results. Serverless technology, Cloud Run, is leveraged to host the microservices-oriented backend.
- Token Storage: stores integration-related tokens in a secure vault, Google Cloud Secret Manager, with very limited access.
- Object Storage: stores objects in buckets on Google Cloud Storage that are not publicly accessible. Each tenant has its own storage bucket.
- Relational Database: stores application-wide (e.g. users, workspaces) information and serves as the application backend database.
- Elasticsearch: stores the minimal information relevant for search and retrieves the search results for a given search query. Elastic Cloud is leveraged for a mananaged Elasticsearch stack.
The environment is hosted in the GCP Region europe-west1, which is located in Belgium.
Multitenancy #
The architecture is multi-tenant, meaning that a single instance of the software and its supporting infrastructure serves multiple customers. Please note that data privacy is respected at all times and is not affected by multi-tenancy.
Data isolation #
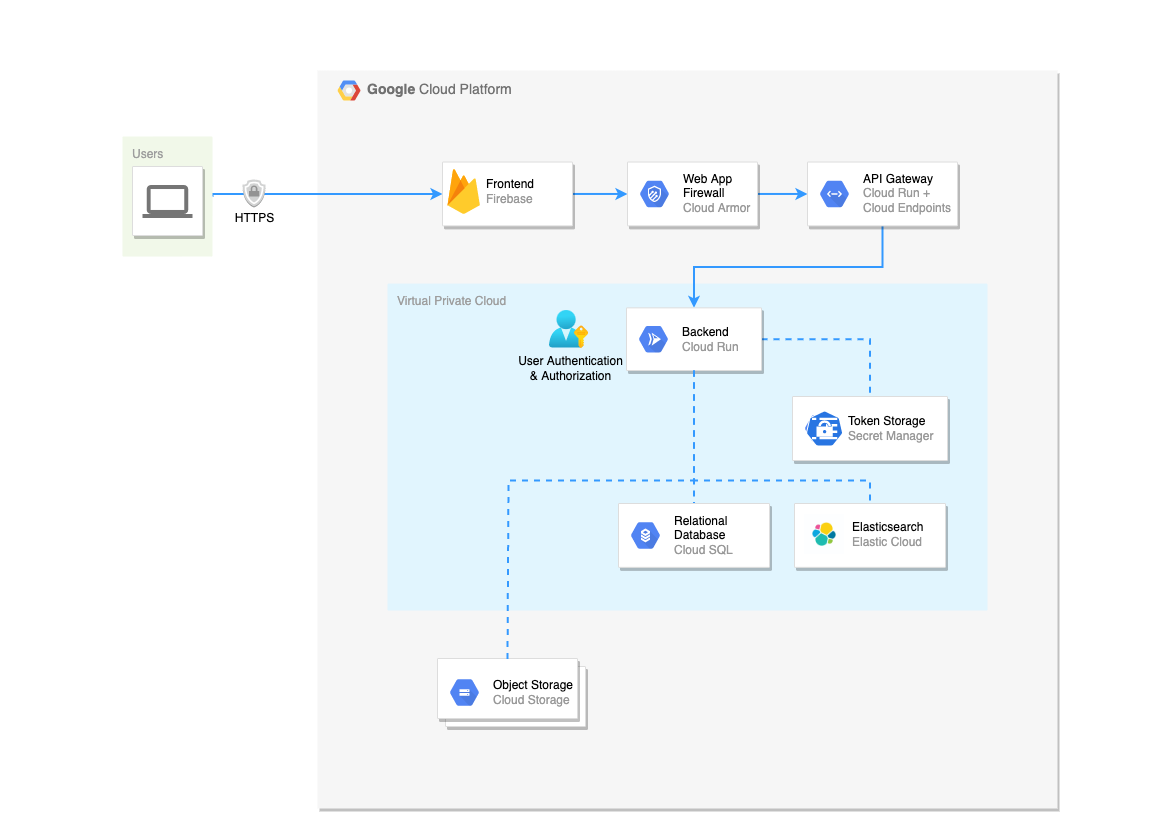
In the multi-tenant architecture, the data is logically separated in the backend layer.
In general, the user is authenticated via the JSON Web Tokens (JWT) and data is restricted to the tenant scope and additionally restricted by mirrored permissions from source document management systems for that user.
For more information on how the data is stored, see Storage layers
More information #
For more information on how integrations are set up, see Integrations.
For more information on how data gets processed and stored, see Data Processing.
For more information on authentication and authorization, see Access Controls.
